The internet, as people know it, exists in layers. Beyond the everyday web of news sites, social media, and streaming services lies a parallel digital universe deliberately hidden from conventional search engines and accessible only through specialized tools. Personal data has become the world’s most valuable and vulnerable commodity in this realm, known as the dark web.
Jason Ho, founder of tech giant Teklium and former designer of microchips for F-35 fighter jets with over 400 patents, demonstrates a technology that could fundamentally disrupt this underground economy of stolen information. The Emulated Quantum Communication (EQC) system doesn’t just aim to keep hackers out; it renders their entire business model obsolete.
EQC: What You Need To Know
At the core of Teklium’s EQC is a framework called Genetic Computing, which assigns unique identifiers to every piece of data created, similar to how DNA distinguishes between our cells and foreign invaders.
Every computing device receives a unique genetic code linked to multiple identifiers: device ID, memory ID, network ID, and MAC address. This multi-layered approach makes unauthorized access exceptionally difficult; without the correct genetic code, the system thwarts infiltration attempts, rendering stolen data useless to cybercriminals.
Teklium’s system incorporates five distinct access categories: private, family, relatives, friends, and public. This provides granular control over who can access specific content while maintaining the read-once principle.
Teklium’s approach fundamentally differs from conventional cybersecurity solutions that have consistently failed to stem the rising tide of breaches. Rather than relying solely on encryption, which can eventually be broken with sufficient computing power, EQC employs principles inspired by quantum mechanics, specifically quantum entanglement.
The technology creates what Ho describes as “an unbreakable bond between data particles across the network. When someone accesses a message or file, this entanglement triggers an irreversible change, making all unauthorized copies instantly inaccessible.”
This isn’t theoretical quantum computing, which requires specialized hardware operating at near-absolute zero temperatures. Instead, EQC emulates quantum principles through sophisticated algorithms running on standard devices.
EQC in Action
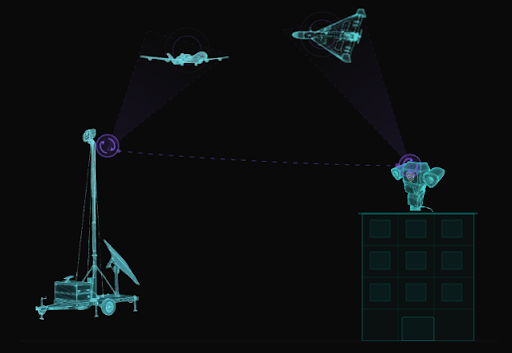
EQC combats dark web operations by fundamentally disrupting the economics of stolen data through its quantum-inspired entanglement protocols. Consider a scenario where hackers breach a credit card information database: traditionally, they would copy this data and sell it multiple times to buyers on dark web marketplaces.
However, with EQC protection, when the first legitimate user accesses their credit card information, all unauthorized copies become automatically invalidated through the system’s entanglement mechanism. Ho explains that this “read-once” technology ensures that stolen copies are rendered worthless before criminals can monetize them. This directly attacks the estimated $8 trillion dark web economy at its foundation by making data theft structurally unprofitable.
The system’s practical impact extends to identity theft prevention through its Meta-AI-powered auto-identification system. When cybercriminals attempt to use stolen credentials protected by EQC, such as login information for financial institutions, quantum-inspired validation requires not just the stolen password but also verification against unique device identifiers (Device ID, Memory ID, Network ID, MAC Address).
Ho explains that without this complete genetic code match, access is denied, and the system immediately alerts the legitimate owner. For instance, the EQC technology nullified the value of 10 million stolen Middle Eastern accounts found on dark web forums, as the data remained inaccessible to buyers despite being technically “obtained,” effectively breaking the supply chain that powers dark web marketplaces.
Ho mentions, “We focused on securing the data, as this is where everything starts. They can’t do anything for the data they can’t access.”
A Big Step Towards a Safer Digital World
Ho quickly points out that the internet’s dark world is far more complex than just a tangle of stolen passwords and pilfered data. He acknowledges that the dark web thrives on many illicit activities, from trafficking in personal identities to the distribution of illegal content and the exploitation of algorithmic manipulation and anonymity.
The founder sees EQC as a decisive tool, but not a single comprehensive solution. He recognizes that while EQC’s structural approach can dismantle the value of stolen credentials and data, it is only one part of a much larger effort required to address the full spectrum of threats lurking in the digital underground. Yet, Ho believes that targeting the password problem is a critical first step in undermining the dark web’s business model.
“Every time we eliminate a password, we take away one more opportunity for exploitation,” he says. EQC’s password-free authentication and read-once data protocols chip away at the foundation of dark web commerce, making it increasingly difficult for criminals to profit from stolen information.
For Ho, this is how real change begins: not by claiming to solve every problem at once, but by systematically brushing off the dark web’s power, one password at a time, until the old ways of digital exploitation become obsolete.